DeFi Rekt Report October 2025: $38.6 Million Lost Across 9 Exploits
October 2025 saw a total of $38.63 million lost across nine distinct security incidents in both centralized and decentralized platforms.
Disclaimer: The information presented in this report is based on data available as of 8/03/2023. Initially, we have reported losses amounting to $486 million [Article] in stolen crypto funds. However, subsequent updates from on-chain research have provided new information indicating that the actual losses are now reported to be $390 million.
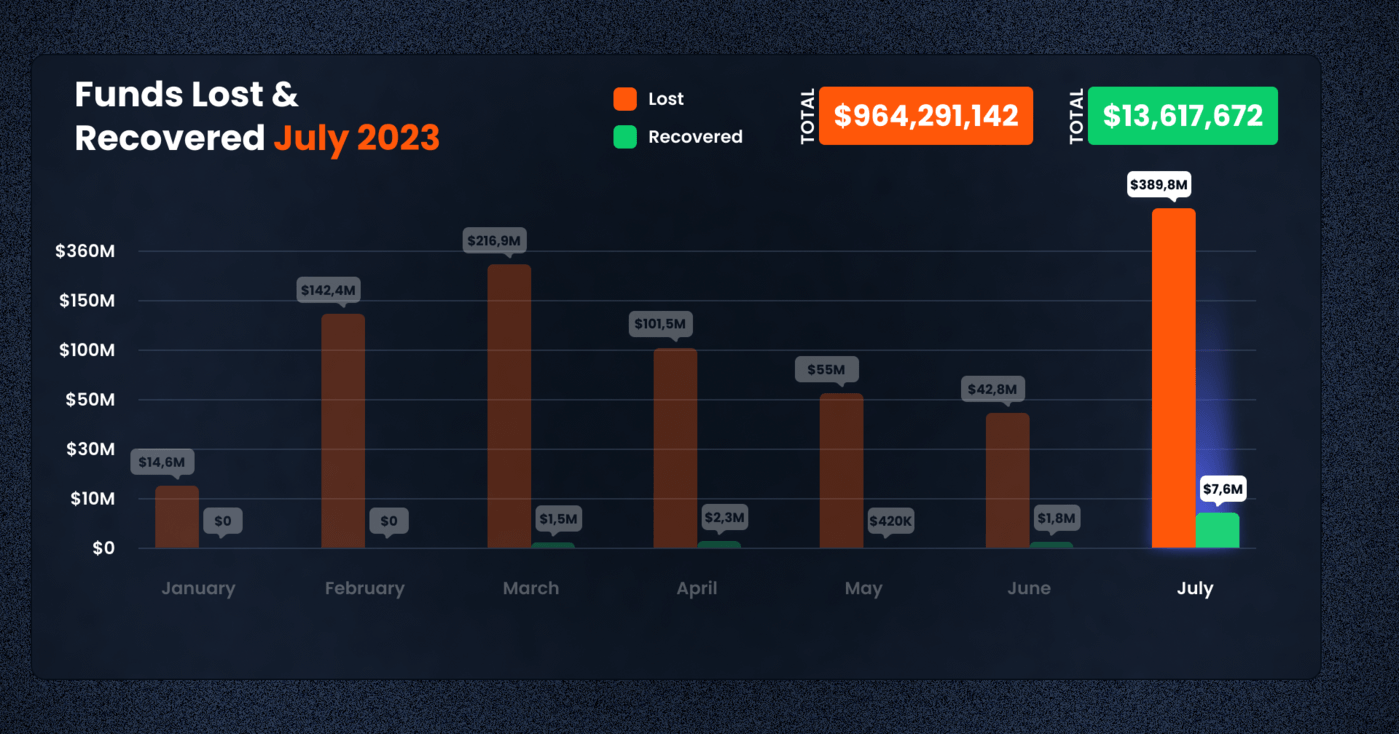
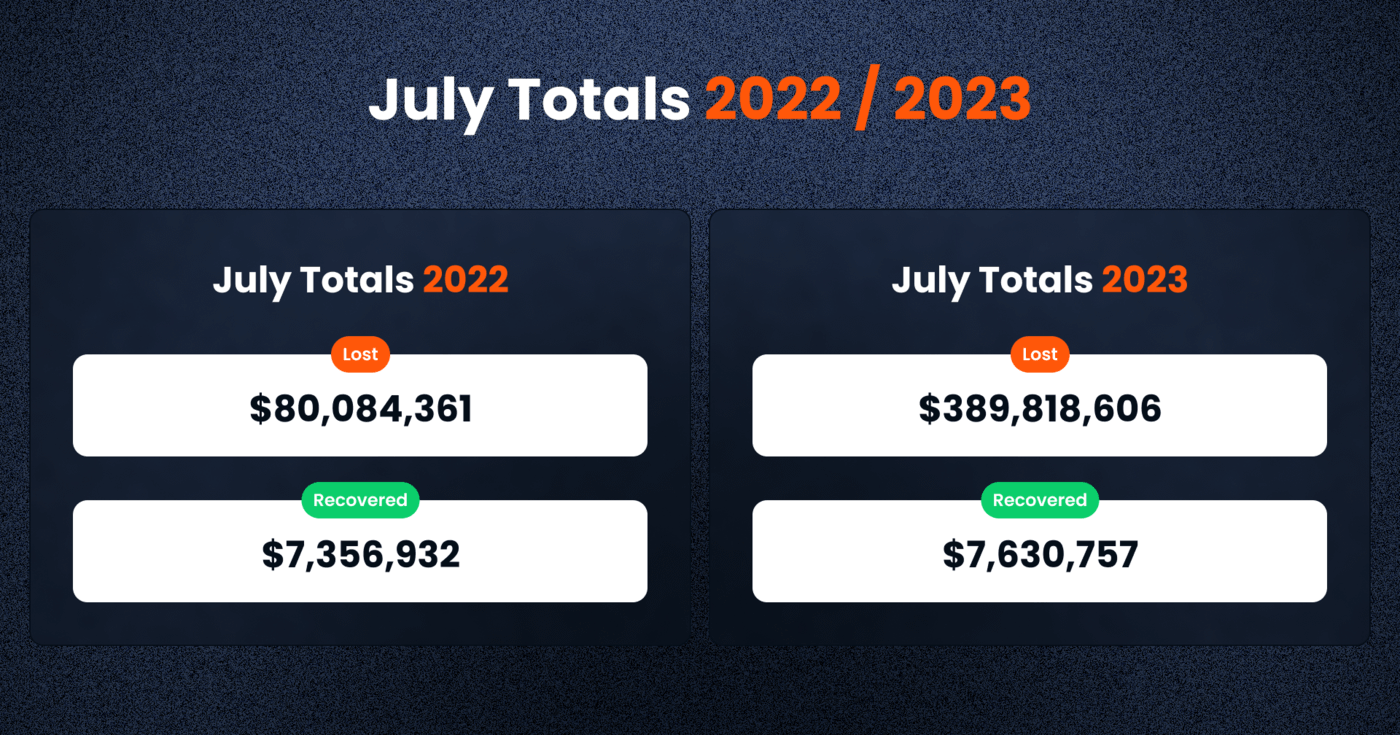
As we move into the second half of the year, July 2023 proved to be a notable period filled with significant cyber-incident-related losses. The tally for the month reached an alarming $389.82 million in funds lost, eclipsing the figure for the same period in 2022, which stood at $80.08 million
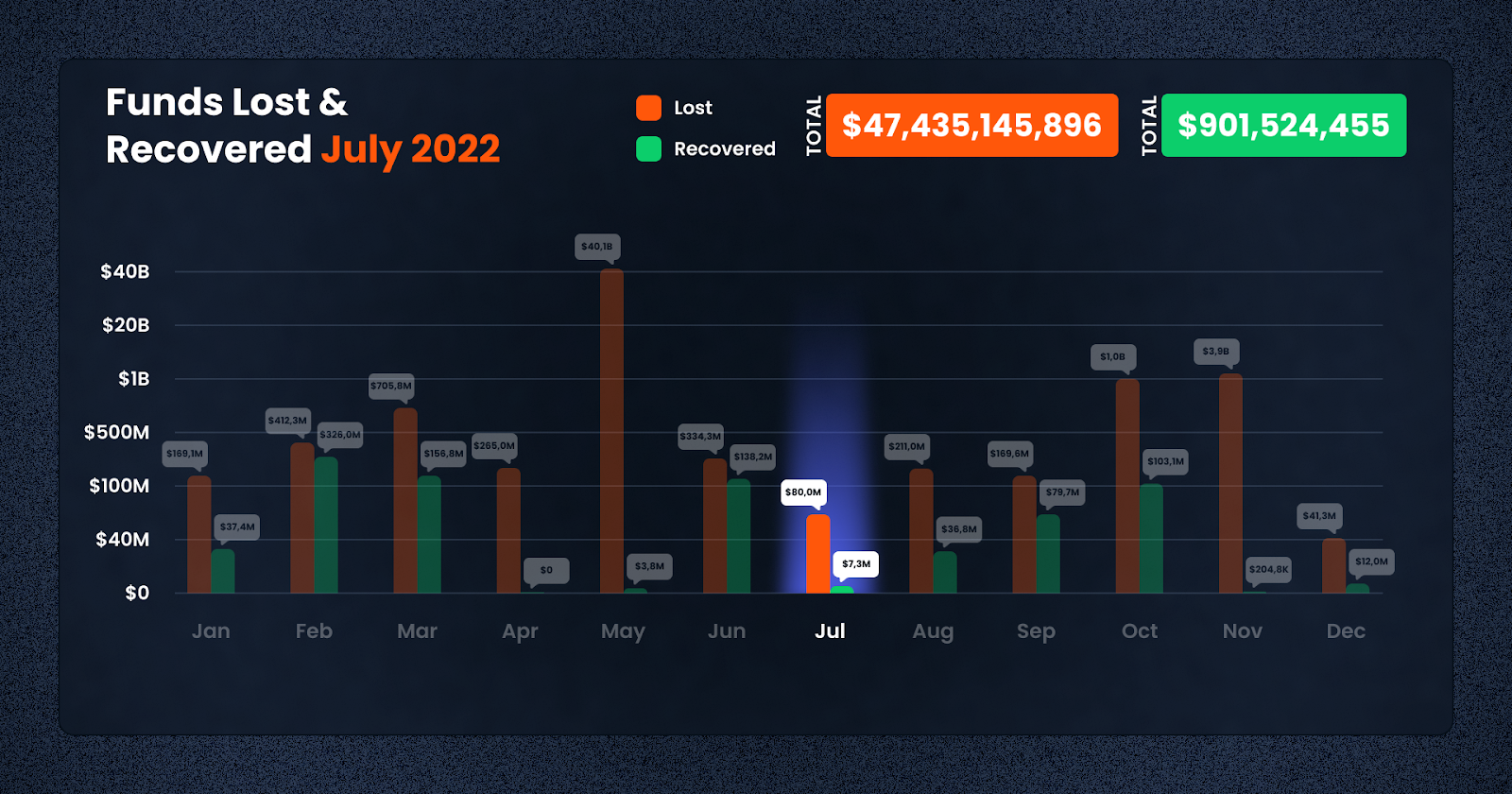
Despite these alarming figures, the recovery rate for the month was dismally low, standing at a mere $7,630,757. In this article, we delve into the details of the month’s losses, highlighting the top ten incidents and examining the context behind these disturbing figures.
While the July 2023 losses significantly exceeded the same month the previous year, they serve as a stark reminder of the continuous challenges the DeFi industry grapples with to ensure robust platform security. Actions taken to fortify security protocols and heighten awareness about potential frauds and scams are progressively crucial in this high-stakes landscape.
Regrettably, the recovery efforts in July 2023 were woefully inadequate, with only $7,630,757 recouped from the vast $389.82 million lost. The ability to recover stolen or lost funds is a pivotal element in alleviating the impact of these unfortunate incidents and crucially, in reinstating faith in the DeFi ecosystem. This highlights the continued challenges that the emerging financial sector faces, even during a period of greater development and interest.
DeFi Exploit Trends: July 2023 Overview
The DeFi landscape in July 2023 witnessed an alarming surge in the total funds lost, a whopping $389,818,606. Ethereum stood as the most targeted platform, with a total loss of $350,659,944 across 36 cases. Binance, another frequently targeted chain, reported a loss of $11,016,822 across 18 cases.
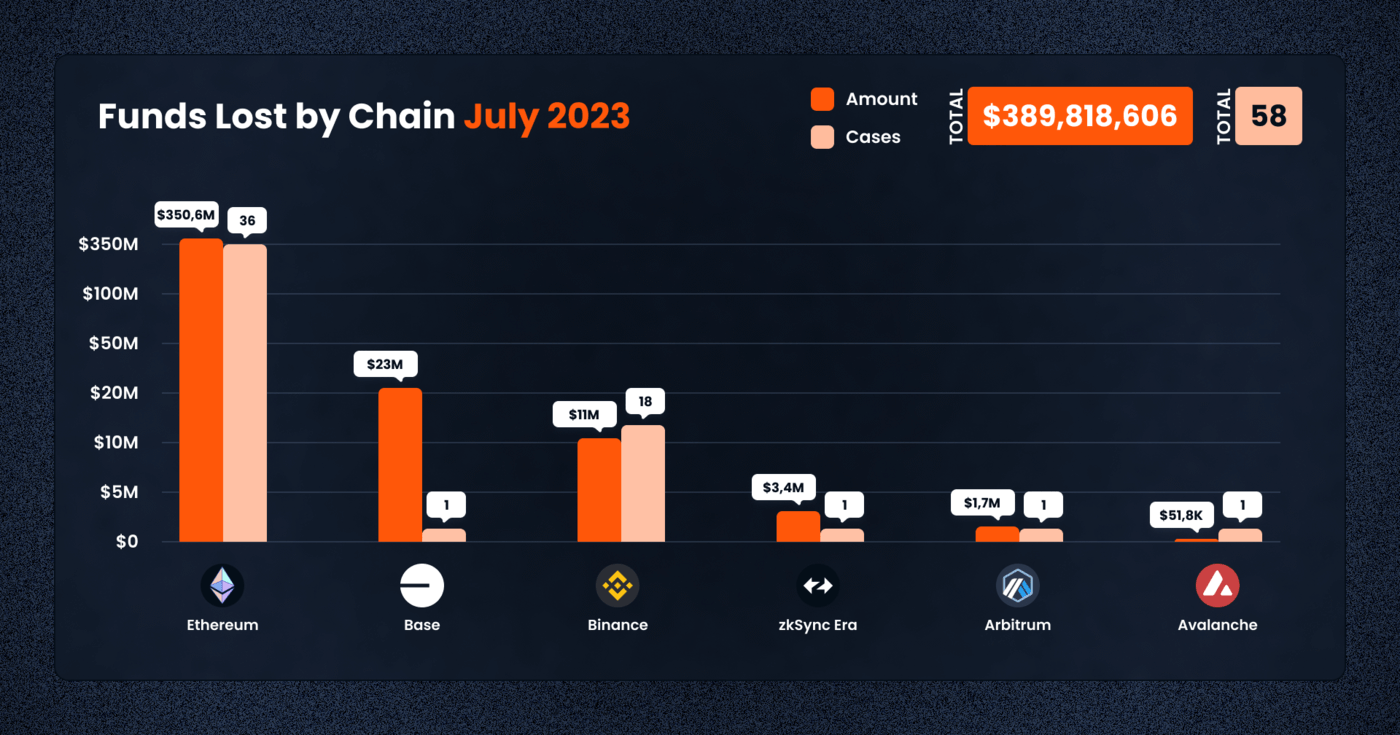
Among the top 10 cases, Multichain experienced the most severe loss of $231m due to an access control exploit. The AlphaPo exploit on the Ethereum platform resulted in a loss of $23m, also due to an access control issue. Over $50m was lost to Vyper Exploit caused by a reentrancy attack .
Other notable cases included GMETA on Binance suffering a loss of $3.7m from a rug pull, Era Lend on zkSync with losses of $3.4m and Conic Finance on Ethereum losing $3.3m to a reentrancy attack, among others.
Types of Exploit
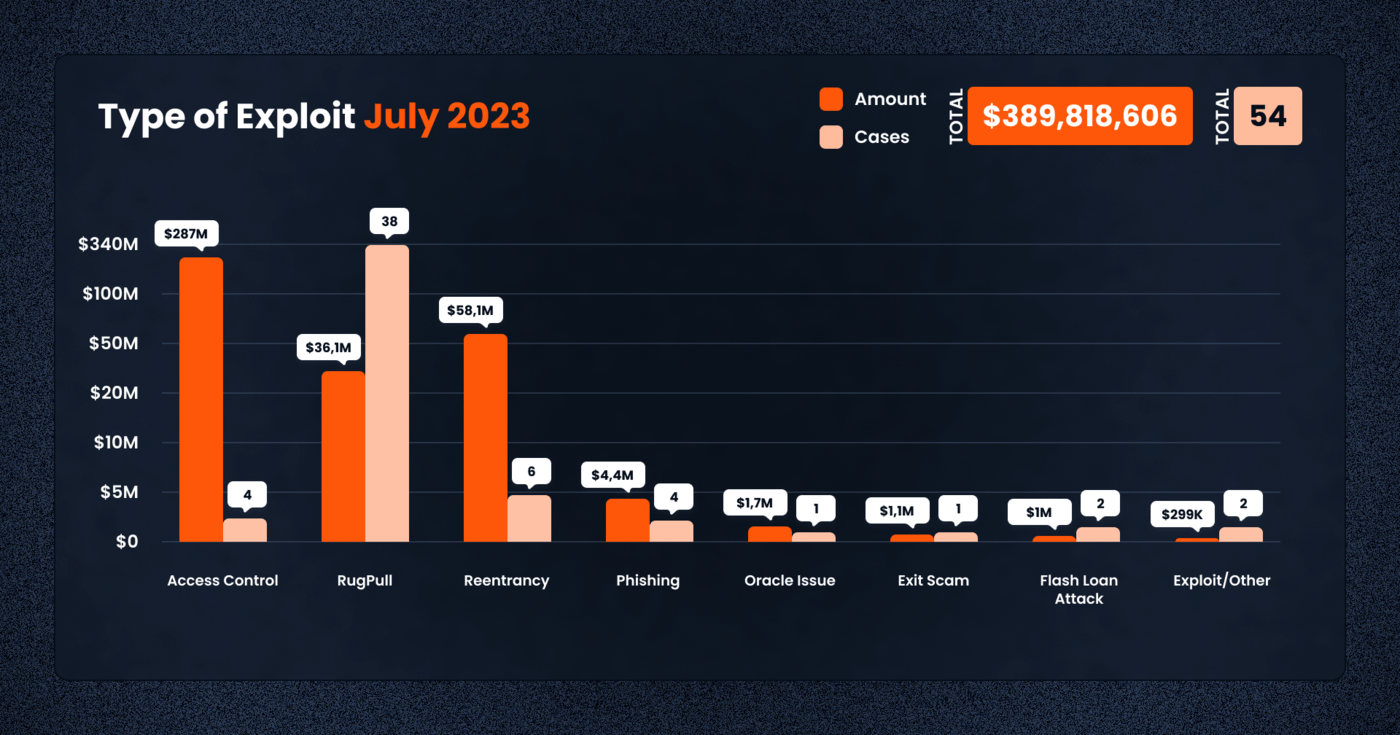
Various types of exploits were employed by crypto criminals in July 2023. Access control issues took the lead, accounting for three major cases but resulting in a staggering loss of $287,034,253.
Rugpulls, despite being the most common with 38 reported cases, resulted in significantly lower losses totaling $36,131,485. Reentrancy attacks, although less frequent with six cases, still led to substantial losses amounting to $58,094,868.
Other exploit types, such as oracle issues and flash loan attacks, were less frequent but contributed to the total loss.
Funds Recovered
Unfortunately, the recovery of exploited funds in July 2023 was drastically low, with only $7,630,757 recouped from the vast total lost.
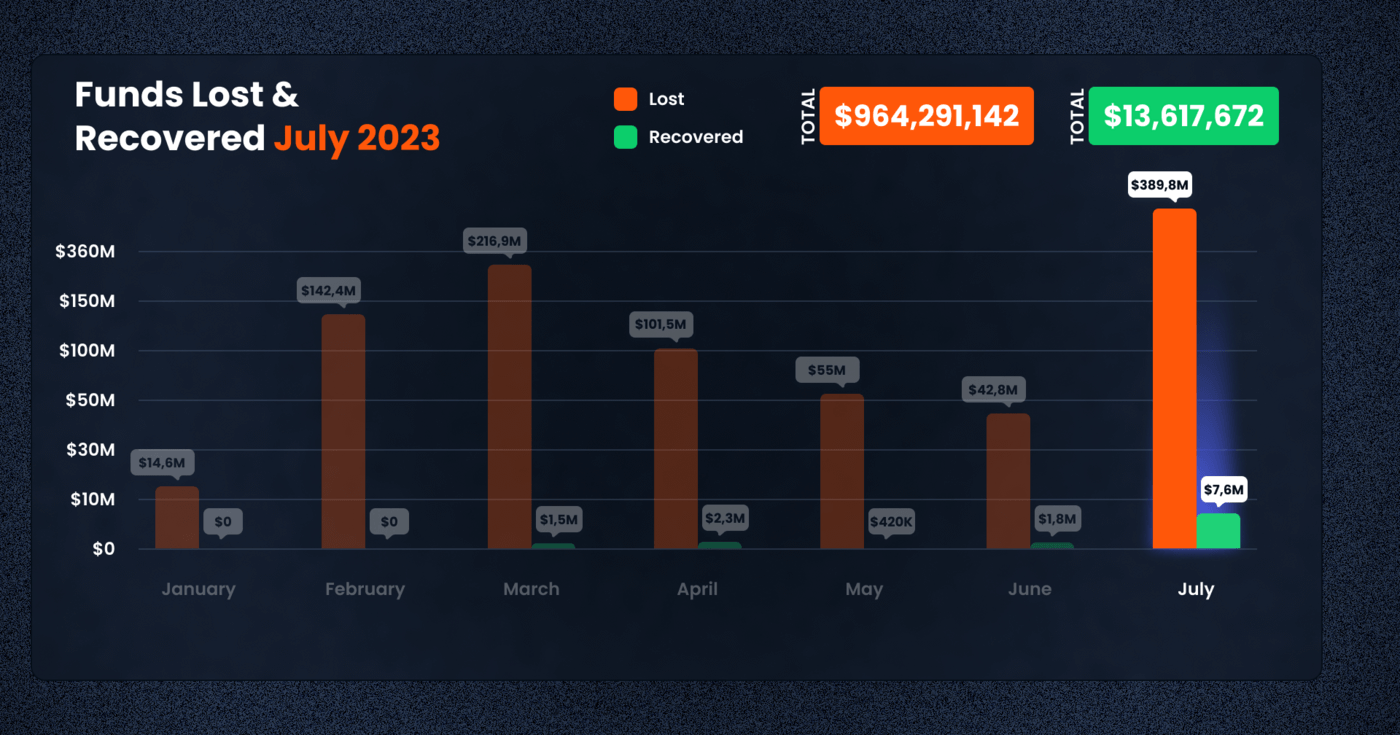
This continues the unfortunate trend of low recovery rates in recent months, highlighting the urgent need for enhanced security measures and investor vigilance in the DeFi landscape.
Attack Vectors
Among the different categories of targets, Tokens were the most frequently attacked, with 39 cases reported leading to losses totaling $35.9m.
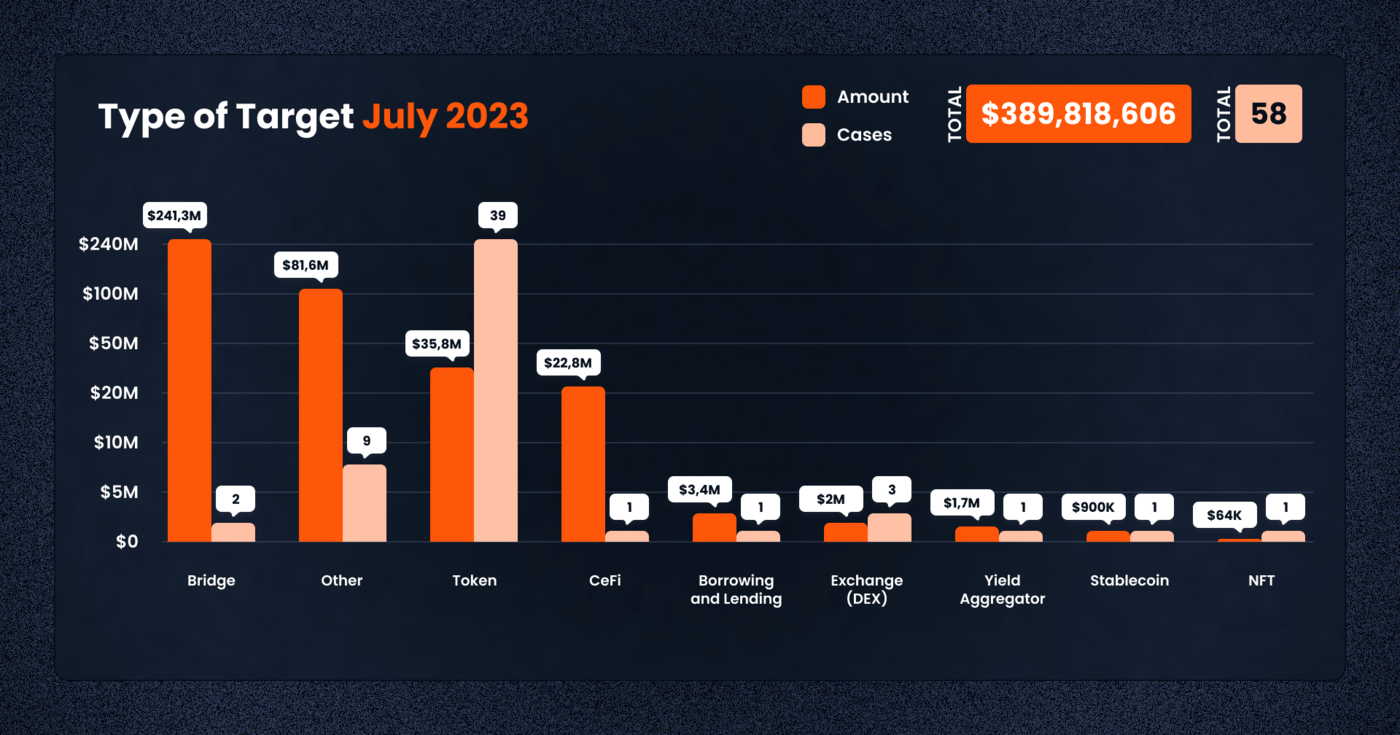
Borrowing and Lending protocols were targeted once, with a loss of $3,400,000. Decentralized Exchanges (DEX) reported losses of $2,010,934 from three incidents.
Notably, the Bridge category was hit hardest, reporting a loss of $241,330,645 from two incidents. Other categories, including CeFi, Yield Aggregators, Stablecoins, and NFTs, were targeted less frequently but still contributed to the total losses.
Top Exploits in July 2023
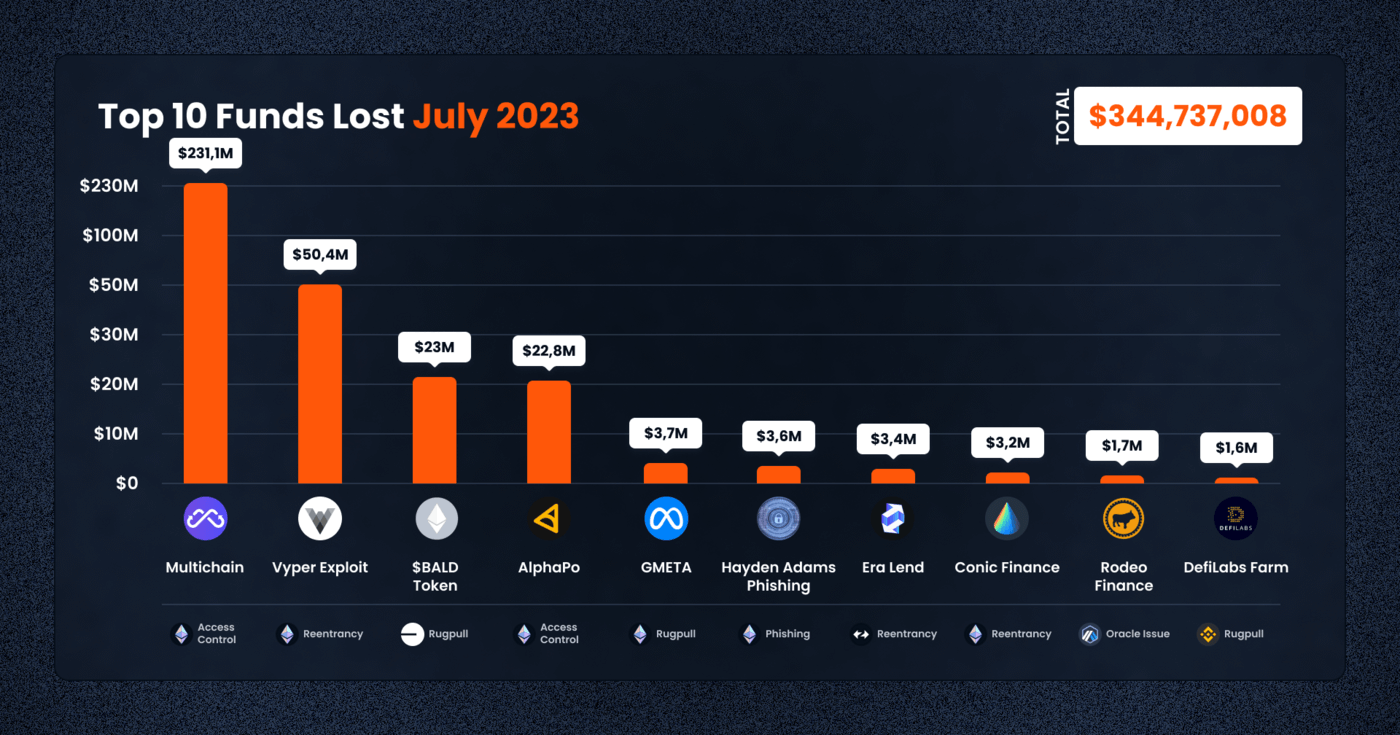
Let’s take a look at the top 5 cases this month:
1. Multichain — $231.1m Lost (Access Control)
On July 10, 2023, the Multichain project, a cross-chain bridge, fell victim to a major exploit. An unauthorized entity successfully gained access to the system, leading to an immense loss of funds across various blockchain networks. The transferred assets were funneled into a single externally owned account (EOA) spread across nine different chains.
The casual pace at which the assets were moved suggested that the perpetrator maintained full control over the funds and was not pressed for time to shift them elsewhere. This behavior fueled speculation that the incident could potentially be an inside job.
The fact that this took place on a cross chain bridge that many smaller chains depended on meant that many ecosystems were severely destabilized.
Here’s an overview of the losses, broken down by blockchain network:
– On the Arbitrum chain, $14,371,766 USD in assets, including USDC, WETH, and WBTC, were lost.
– Fantom reported a loss of $48,560,731 USD in assets, including USDC, WETH, DAI, WBTC, and over 60 million non-liquid fUSDT tokens.
– On the Optimism network, assets lost totaled $11,080,749 USD, consisting of USDC, DAI, and WBTC.
– Cronos reported a loss of $10,911,004 USD in assets, including USDC, WETH, and DAI.
– The Polygon network experienced a loss of $10,990,882 USD in assets, comprising USDC, WETH, and WBTC.
– Avalanche saw losses of $3,190,649 USD, specifically in DAI and WBTC.
– Binance Smart Chain reported a loss of $1,770,304 USD in USDC and BTCB assets.
– The Moonbeam network lost $237,657 in USDC.
– Finally, on the Ethereum network, there was a loss of $15,291 USD in DAI.
In total, the theft of liquid assets amounted to approximately $101,129,033 USD, leading to an estimated total loss for Multichain of $231,000,000 USD.
Delving into the details of the exploit, it was discovered that around $130 million was extracted from various token bridges. The assets held in the Multichain multi-party computation (MPC) address were unusually moved to an EOA address.
The unexpected withdrawals resulted in the depletion of the entire holdings of Multichain’s Fantom Bridge, which included wBTC, USDC, USDT, and a selection of altcoins, amounting to over $130 million in total. Similar withdrawals were witnessed from the Multichain’s Moonriver and Dogecoin bridge contracts.
The transferred assets from the Fantom bridge of Multichain comprised DAI, LINK, USDT, wBTC, wETH, and USDC. Following the incident, the Multichain team announced their uncertainty regarding the cause of the exploit. Although a compromised wallet was speculated to be the most likely cause, the possibility of an insider hack has not been ruled out.
Block Data Reference
Suspicious Addresses:
https://etherscan.io/address/0x418ed2554c010a0c63024d1da3a93b4dc26e5bb7
https://etherscan.io/address/0x027f1571aca57354223276722dc7b572a5b05cd8
Fund Movement Transactions:
https://etherscan.io/tx/0xda80a8c8d5a8fdf0208a6fd01c39af018e400763b1d08f3543f52353345fe62e
https://etherscan.io/tx/0xbd29fe07555c28527fb0207aa0ac2b67d4afef0426793c35b76d005613477fc4
2. Vyper Compiler — $50.5m Lost (Reentrancy)
The Vyper Compiler, a widely used tool for developing smart contracts on EVM-compatible chains, experienced a severe security breach due to a vulnerability present in versions 0.2.15 to 0.3.0. Independent security researchers have confirmed that the issue was addressed and resolved in version 0.3.1. The exploit leveraged this vulnerability to execute a reentrancy attack on several projects, leading to a staggering combined loss of 50,476,970 USD. While efforts were made to recover some of the funds, the impact on projects such as MetronomeDAO, JPEG’d, Alchemix, and Curve Pools was significant.
The vulnerability within the Vyper Compiler lay in versions 0.2.15 to 0.3.0. During a thorough investigation conducted by independent security researchers, it was found that the root cause of the exploit was the presence of separate Reentrancy Lock slots within the add_liquidity and remove_liquidity functions in Curve Pools. These functions were implemented in the vulnerable versions of the Vyper Compiler, inadvertently exposing them to potential reentrancy attacks. A reentrancy attack is a malicious technique wherein an attacker can repeatedly call a function within a smart contract before it completes its execution, exploiting the contract’s state and potentially causing financial losses.
The exploit that emerged from this vulnerability had detrimental consequences for several blockchain projects, causing a total loss of 50,476,970 USD. Among the affected projects were:
Upon the discovery of the exploit, affected projects and developers quickly took action to mitigate the damage and recover funds where possible. A total of 6,820,757 USD was successfully recovered and returned to the impacted projects.
Block Data Reference
Exploiters:
https://etherscan.io/address/0xb752def3a1fded45d6c4b9f4a8f18e645b41b324
https://etherscan.io/address/0xc0ffeebabe5d496b2dde509f9fa189c25cf29671
Malicious Transactions:
https://etherscan.io/tx/0xcd99fadd7e28a42a063e07d9d86f67c88e10a7afe5921bd28cd1124924ae2052
https://etherscan.io/tx/0x2e7dc8b2fb7e25fd00ed9565dcc0ad4546363171d5e00f196d48103983ae477c
3. BALD Token — $23.1m Lost (Token Rugpull)
The Bald token, a project hosted on Coinbase’s Base chain and available for trading on LeetSwap, suffered an exit scam perpetrated by its own deployer. The exploit involved the deployer’s orchestrated removal of liquidity from the LP (Liquidity Provider) pool in a series of transactions. Among these transactions, the final four removals amounted to 10,804 ETH, which was valued at approximately 19,930,848 USD based on prevailing exchange rates at the time of the rugpull.
As of July 31, 2023, the ill-gotten funds remain in the scammer’s original address. Consequently, the scammer now wields control over 12,059 ETH, which is equivalent to $23.1m USD.
In the aftermath of the exploit, the official tweet from the Bald token project claimed that no tokens were sold during the rugpull. Instead, the scammer solely focused on adding and removing liquidity from the LP pool. However, the community and investors have expressed significant concern over the loss of liquidity and the impact it has on the project’s viability.
Block Data Reference
Attacker Addresses:
https://etherscan.io/address/0xe0Afadad1d93704761c8550F21A53DE3468Ba599
https://etherscan.io/address/0x8E0001966e6997db3e45c5F75D4C89a610255b2E
https://etherscan.io/address/0xdddE20a5F569DFB11F5c405751367E939ebC5886
Malicious Transaction Examples:
https://etherscan.io/tx/0xe280153aa5d9c6cc3aa2ae6713ad8f91889fa6007485eb54318bd957b74776da
https://etherscan.io/tx/0x0a751caedcf4a53f13d7343989a3380da48ff09412afcb144ce4c249fc99263d
https://etherscan.io/tx/0x3a6e5d7e1b9386940b1db81d4e514cbaf5986963f3124dd7eb2a06989890f993
4. AlphaPo — $22.8m Lost (CeFi, Access Control)
In July 2023, the crypto payment platform AlphaPo suffered a significant security breach. This resulted in a substantial loss of approximately $22.8 million across Bitcoin, Tron, and Ethereum blockchains. AlphaPo, which processes payments for multiple gambling services, experienced an exploit that targeted their hot wallets on the Bitcoin, Tron, and Ethereum chains. The breach was primarily attributed to a compromised private key.
As part of the exploit, the stolen assets were initially converted into 5,742 ETH. These funds were then routed to the Avalanche blockchain via several addresses. Upon reaching Avalanche, the assets were exchanged once again for BTC and subsequently bridged to the Bitcoin chain.
Simultaneously, on the Tron chain, the looted funds were swapped for 118,482,405 TRX and then distributed through multiple addresses.
The confirmed loss of $22,851,804 USD spanned across the Ethereum and Tron blockchains as follows:
On the Ethereum chain, approximately $10,716,942 USD worth of assets were stolen.
Simultaneously, the Tron chain saw losses amounting to $12,134,862 USD.
Although the confirmed loss is currently estimated at around $23 million, it is worth noting that this figure could potentially reach up to $100 million. This is due to the fact that the exact extent of the losses incurred on the Bitcoin chain has not yet been revealed.
Block Data Reference
Attacker Addresses:
https://etherscan.io/address/0x040a96659fd7118259ebcd547771f6ecb9580d17
https://etherscan.io/address/0x6d2e8a20b8afa88d92406d315b67822c01e53c38
https://etherscan.io/address/0x8dc4f02e620fb24d07208c09950b9cba343805e8
https://tronscan.org/#/address/TKSitnfTLVMRbJsF1i2UH5hNUeHLDrXDiY
https://tronscan.org/#/address/TDoNAZHa7WxarUAFbQUhiijTGtd7EpbzRh
5. Poly Network — $10.2m Lost (Access Control)
On 1 July 2023, Poly Network, a cross-chain bridge, fell victim to a security exploit. This led to the loss of 5,196.95 ETH, which amounted to approximately $10,201,612 USD.
The incident at Poly Network was triggered by a security lapse in access control. The attacker managed to generate signatures, likely using the project’s wallets, which led to a significant drain of diverse assets across multiple chains. These chains included Ethereum, Binance Smart Chain, Avalance, and Metis.
Following the initial attack, the exploiter executed a large-scale swap of SHIB and other liquid assets for ETH. They also managed to drain USDC and USDT in two subsequent attacks, which were then exchanged for ETH. Cumulatively, the exploit resulted in the theft of 5,196.95 ETH, equivalent to approximately $10,201,612 USD.
It is noteworthy that the stolen assets were not limited to ETH but also incorporated non-liquid ERC20 tokens. Consequently, the total value of the pilfered assets across various chains significantly surpassed the actual funds lost. However, due to low liquidity, the attacker was unable to cash out these assets. Nevertheless, assets worth approximately $18,444,696 USD were distributed amongst 17 EOA addresses, each alongside 1 ETH, suggesting a potential future cash out.
Block Data Reference
Attacker Addresses:
https://etherscan.io/address/0xe0Afadad1d93704761c8550F21A53DE3468Ba599
https://etherscan.io/address/0x8E0001966e6997db3e45c5F75D4C89a610255b2E
https://etherscan.io/address/0xdddE20a5F569DFB11F5c405751367E939ebC5886
Malicious Transactions:
https://etherscan.io/tx/0xe280153aa5d9c6cc3aa2ae6713ad8f91889fa6007485eb54318bd957b74776da
https://etherscan.io/tx/0x0a751caedcf4a53f13d7343989a3380da48ff09412afcb144ce4c249fc99263d
https://etherscan.io/tx/0x3a6e5d7e1b9386940b1db81d4e514cbaf5986963f3124dd7eb2a06989890f993
Conclusion
The substantial financial losses recorded in July 2023 underscore the critical need for enhanced risk management and vigilance when interacting with the Decentralized Finance (DeFi) landscape. It is incumbent upon investors to acquaint themselves with potential vulnerabilities and to strategize effectively to secure their investments. At De.Fi, we understand the pivotal role that guidance and support play in traversing the complex and evolving DeFi ecosystem. As such, we remain devoted to equipping our users with useful resources and data to empower informed investment decisions in the field.
*It is important to consider that figures and data related to cryptocurrency hacks can be subject to revisions and updates due to ongoing on-chain investigations, analysis and market price changes. Therefore, readers are advised to exercise caution and verify the latest information available such as tracked in our Rekt Database.
October 2025 saw a total of $38.63 million lost across nine distinct security incidents in both centralized and decentralized platforms.
The third quarter of 2025 marked yet another turbulent period for the DeFi and wider crypto ecosystem, with $434,124,000 lost to exploits, scams, and security failures across both centralized and decentralized platforms.
June 2025 witnessed another alarming month for Web3 security, with a total of $114,768,000 lost during 11 separate attacks
May 2025 saw both DeFi and CeFi security once again under attack, with $275,953,000 lost across just 8 recorded incidents
April 2025 witnessed a large escalation in exploit volume and value, with a massive $5,919,684,000 being stolen in 10 confirmed events.
Q1 2025 marked one of the worst quarters in blockchain exploit history, with total recorded losses topping $2,052,584,700 across 37 incidents
© De.Fi. All rights reserved.