DeFi Rekt Report October 2025: $38.6 Million Lost Across 9 Exploits
October 2025 saw a total of $38.63 million lost across nine distinct security incidents in both centralized and decentralized platforms.
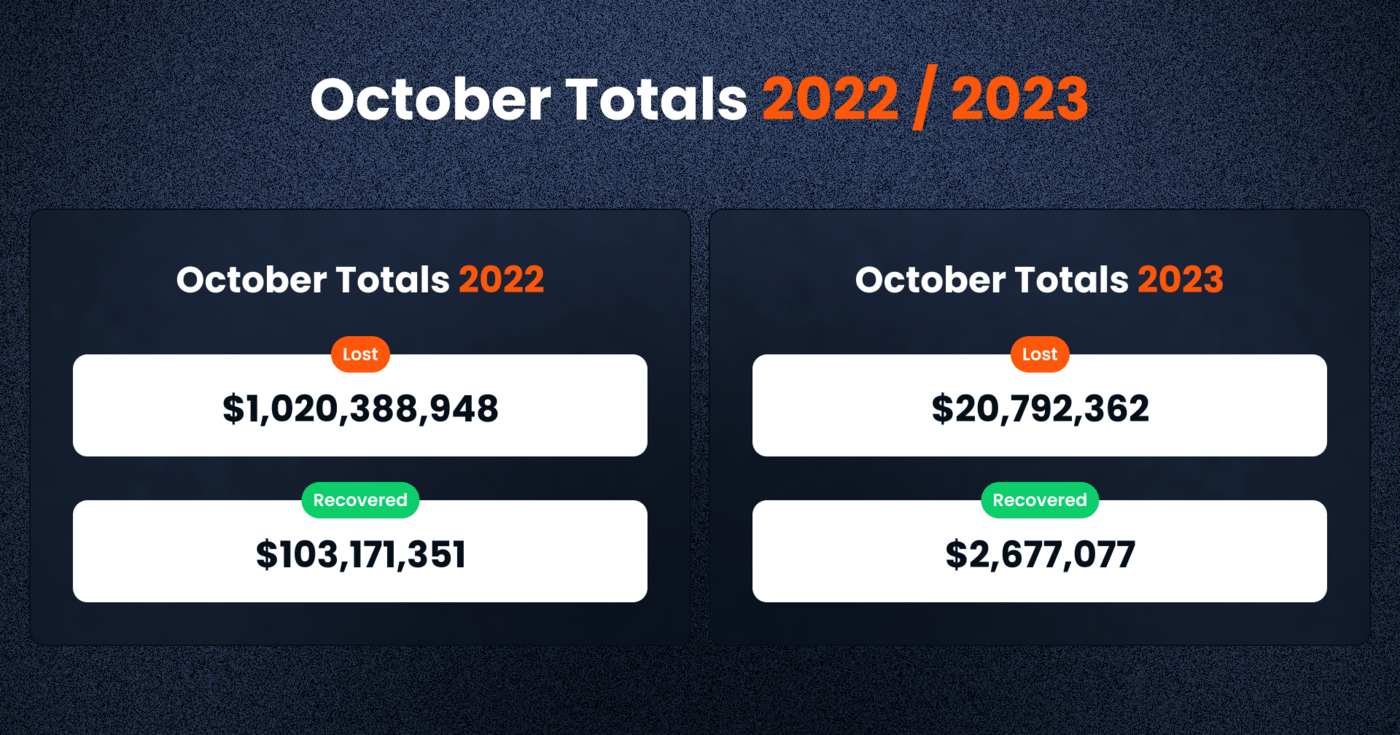
The DeFi sector in October 2023 was not insulated from the perpetual threat of bad actors and cyber-attacks, with over $20 million lost to various exploits. Nevertheless, concerted recovery efforts were fruitful, clawing back approximately $2.67 million—just under 10% of the amount lost. This shows the challenges faced when attempting to reverse incidents of losses in the crypto space, where transactions are anonymous and final.
Here is a look at the numbers:
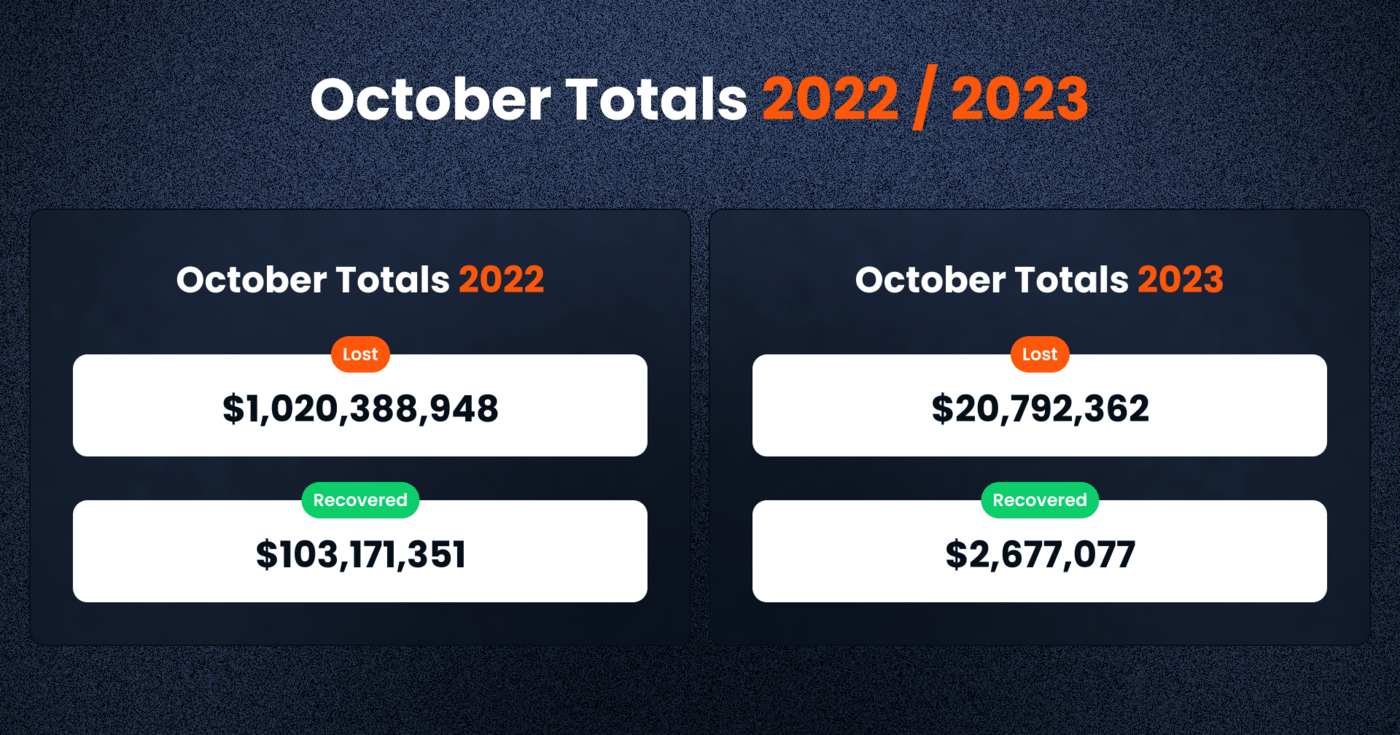
The comparison between October 2023 and October 2022 provides a snapshot of the security situation in the DeFi sector. In October 2022, the DeFi space was reeling from a massive loss of over $1 billion, a figure that dwarfs the $20,792,362 lost in October 2023. This year-on-year decrease suggests that the industry may be making headway in implementing more effective security measures and fostering a culture of diligence among users and developers alike, but could also be driven by the reduced activity in the space this year.
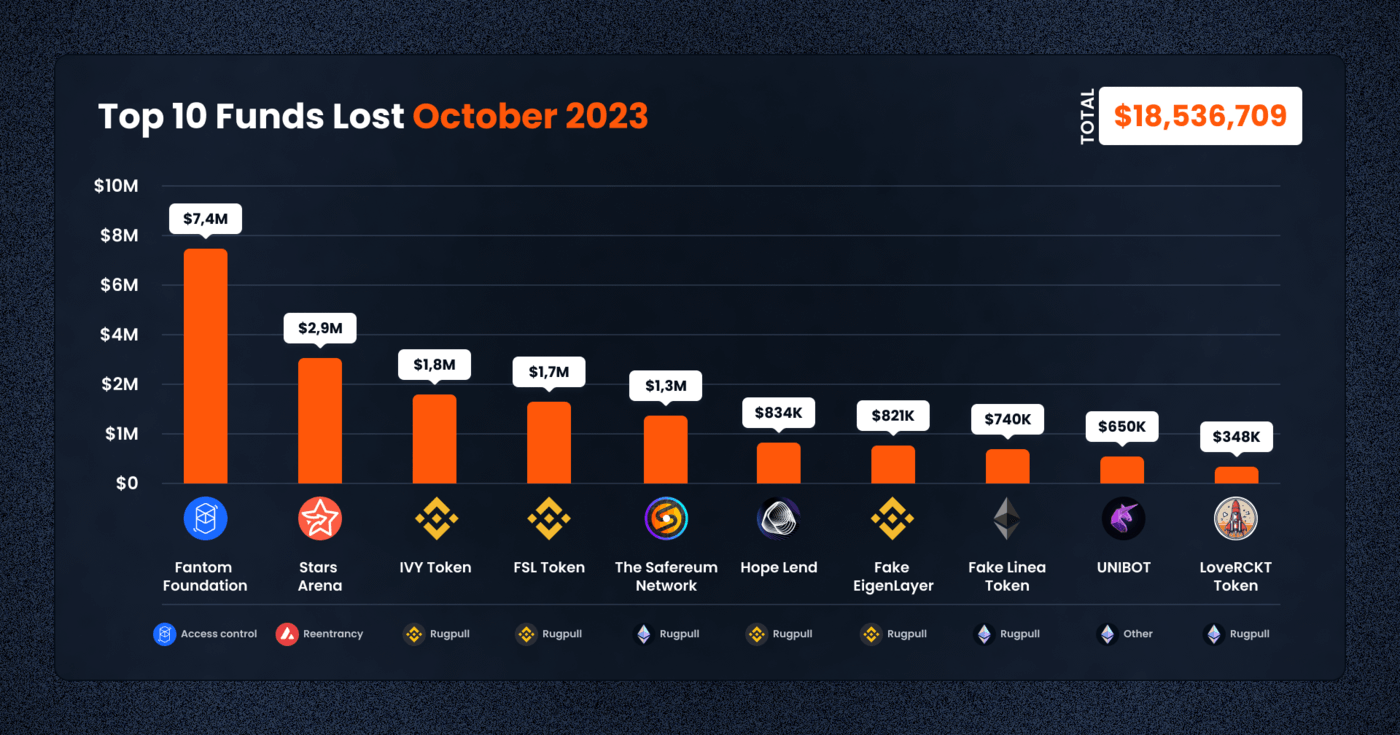
The DeFi space in October 2023 witnessed a number of high profile exploits, cumulatively resulting in the loss of $20,792,362.
A closer inspection of October’s numbers reveals that losses were not uniformly distributed across blockchain networks, nor were they caused by a single type of exploit.
The Fantom chain encountered the most severe loss of $7.35 million due to an access control breach impacting the Fantom Foundation, a reminder of how no DeFi protocols is fully immune. This was in fact the largest individual loss ever recorded on the Fantom chain, which has been popularized by its low fees and fast transaction speeds.
Similarly, the Avalanche chain was not spared, with Stars Arena suffering a loss of nearly $3 million due to a reentrancy exploit. This type of attack remains a considerable concern, as it involves exploiting the vulnerabilities inherent in smart contract execution sequences.
In terms of frequency of loss events, the Binance BNB chain, a hub for numerous DeFi projects, unfortunately led the way again. It saw a cumulative loss of $5.68 million from 15 separate incidents, with many exploits classified as rug pulls. This category of exploit, where developers abandon a project and abscond with funds, accounted for a loss of $1.82 million by IVY and $1.68 million by FSL, marking a worrying trend that tarnishes investor trust.
Similarly, Ethereum, despite its position as the original, leading DeFi platform, was not impervious to exploits. It suffered 14 incidents with a total loss of $4.77 million. The continued targeting of Ethereum-based protocols underscores the chain’s substantial share in the DeFi market and its attractiveness to malicious entities.
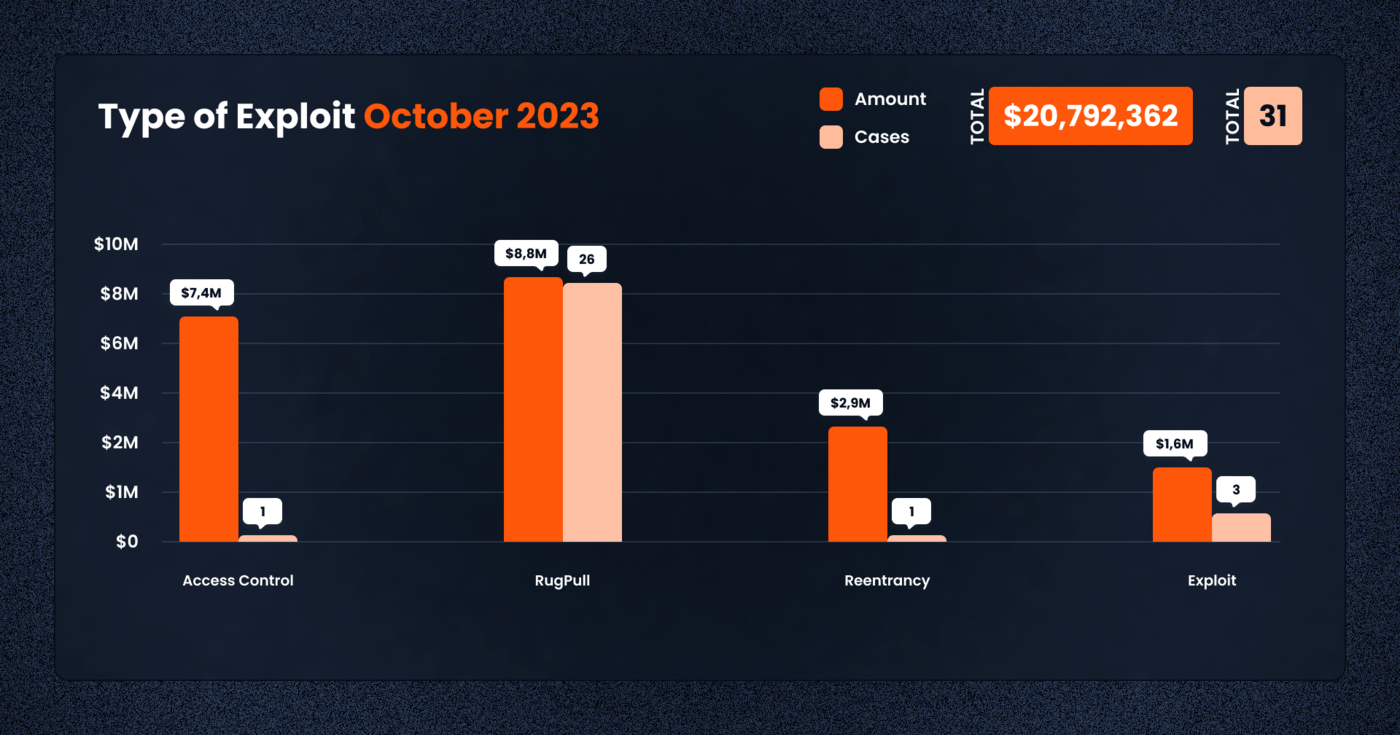
October’s ledger of DeFi exploits categorizes the incidents into several alarming types. Rug pulls continue to be the most prevalent form of exploit, with 26 cases accounting for $8,817,744 lost. This form of exploit, where developers prematurely withdraw funds and abandon the project, indicates a need for enhanced due diligence and investor education in project selection.
Access control issues, although less frequent, resulted in a significant single-event loss of $7,359,282. This single large loss within the Fantom Foundation underscores the critical importance of stringent access protocols and the dire consequences of their oversight.
Similarly, reentrancy attacks, though registering only one case, led to a substantial loss of $2,974,530. These sophisticated attacks exploit contract interdependencies and call attention to the need for rigorous smart contract auditing.
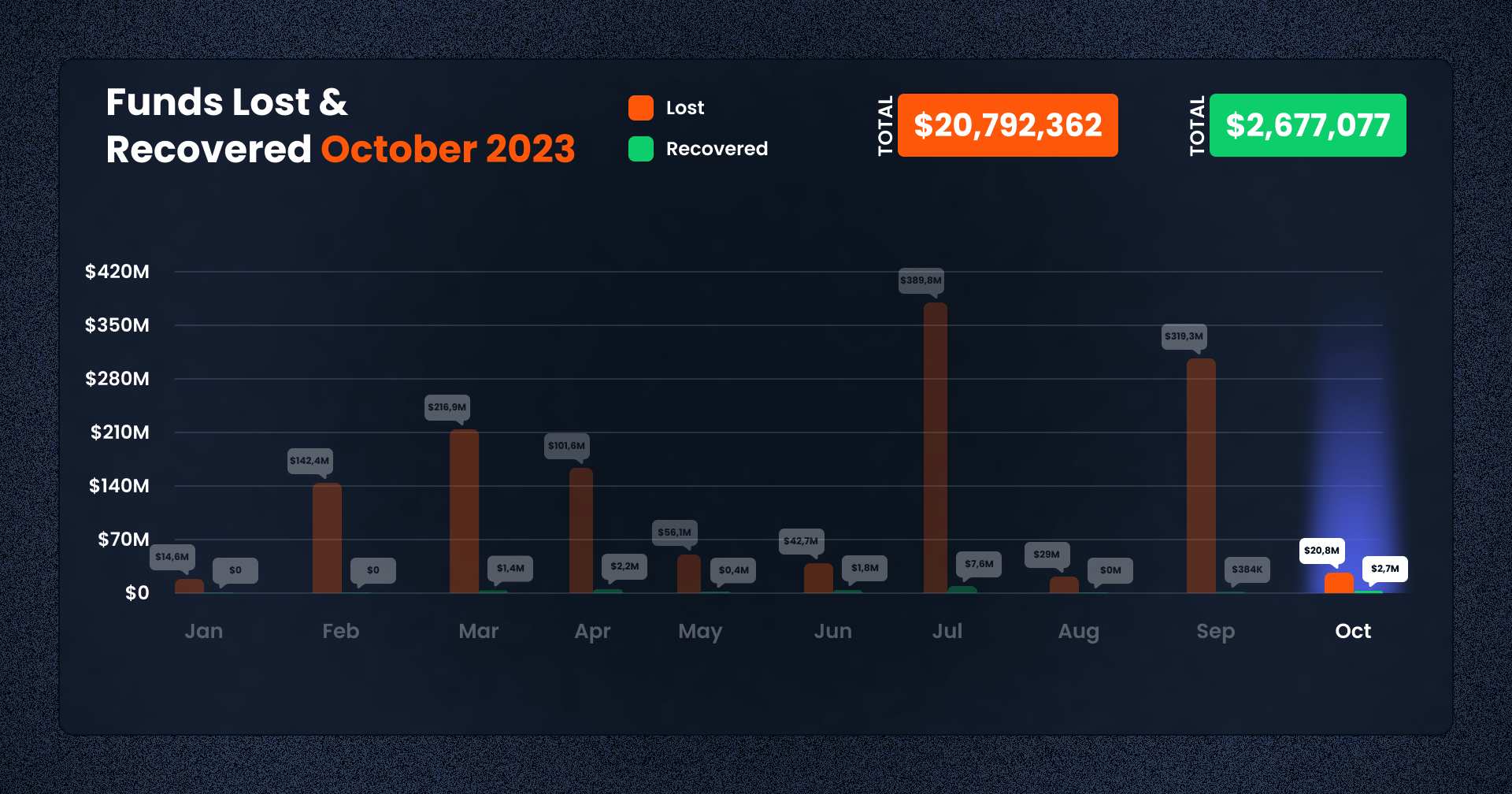
October 2023 marks a modest step forward in the DeFi sector’s recovery efforts with the successful recovery of $2,677,077 out of the $20.8m lost. This recovery, albeit modest compared to the total losses, demonstrates the sector’s resilience and the effectiveness of the emerging security measures and tracing mechanisms.
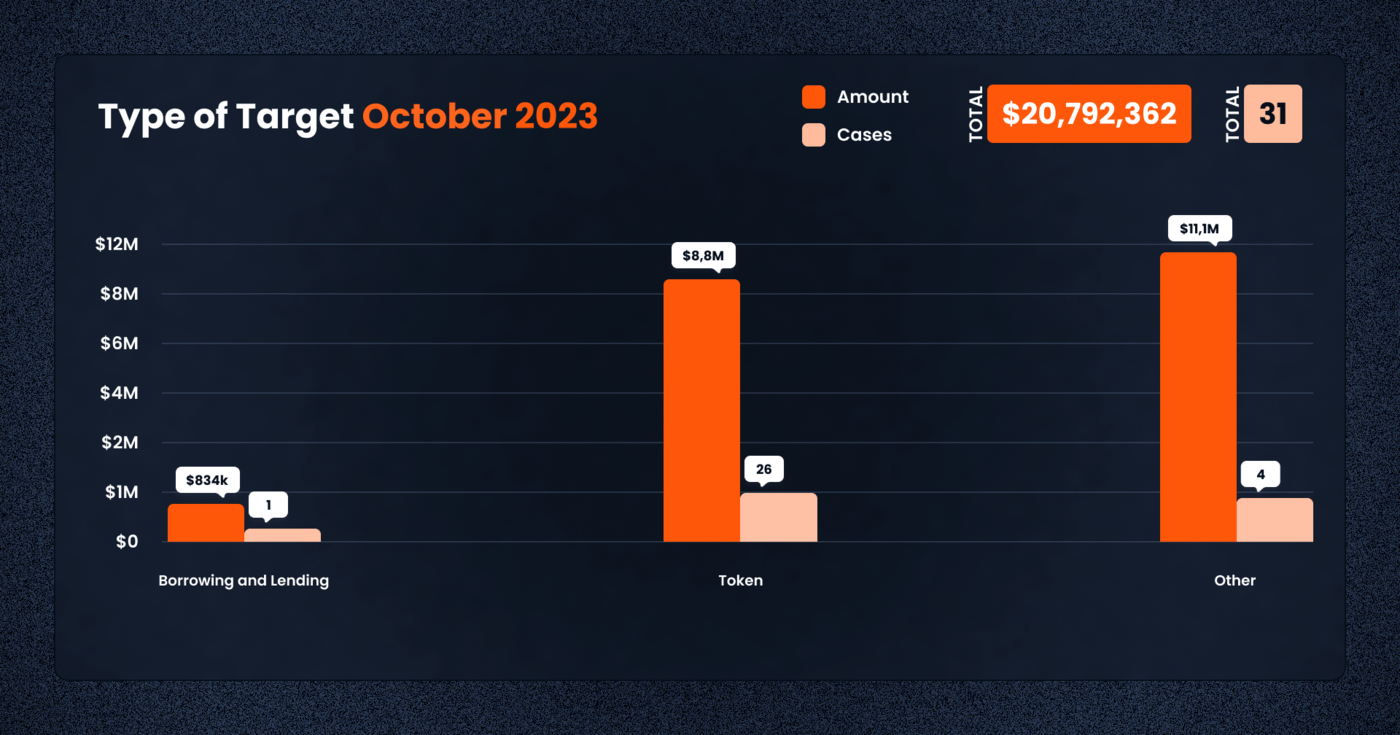
In October 2023, the DeFi ecosystem encountered a diverse array of attack vectors, with varying degrees of frequency and financial impact across different categories. The breadth of these attacks demonstrates the multifaceted nature of the security challenges that DeFi protocols face.
In the borrowing and lending category, a critical component of the DeFi infrastructure, there was one notable incident leading to a loss of $834,616. While the frequency was low, the occurrence of such an incident is a reminder of the risks associated with staking funds on borrowing and lending protocols.
Tokens remained a prime target for nefarious activities, with 26 incidents amounting to a loss of $8,817,744. The prevalence of token-related exploits points to the ever present issue with token security, emphasizing the importance of due diligence and the need for enhanced protective measures for token holders and traders.
Let’s take a look at the top 5 cases this month:
1. Fantom Foundation — $7.4m Lost (Access Control)
This October, the Fantom Foundation fell victim to an attack that resulted in losses exceeding $7 million. The incident involved the exploitation of wallets associated with the Foundation, with the bulk of the stolen funds traced back to one of its employees. The initial analysis suggested that the attack could be attributed to a vulnerability in Google Chrome—potentially a zero-day or a known heap overflow vulnerability identified as CVE-2023-4863.
The Fantom Foundation has confirmed that around $550,000 of the stolen amount was directly from its reserves, while the remaining sum belonged to the affected employee. The precise attack vector remains under investigation as the Foundation and security experts seek to uncover the full scope and method of the attack.
Block Data Reference
Attackers:
https://ftmscan.com/address/0x1d93c73d575b81a59ff55958afc38a2344e4f878
https://etherscan.io/address/0x1d93c73d575b81a59ff55958afc38a2344e4f878
https://etherscan.io/address/0x2f4f1d2c5944dba74e107d1e8e90e7c1475f4001
Funds Transfer Transactions:
https://etherscan.io/tx/0xf574dde03c60c5c9d78e51f730ac3b808c9a6e100e8b8fde68a3ac8f557805f8
Malicious Transactions:
https://ftmscan.com/tx/0xa7c3d133006f66ab62aa92fd851bd4d2452bbd9c50a368cbf283230a42c60ac3
https://ftmscan.com/tx/0x334f62e08f0d7e3427a5efaa926fe8353bf92d6f3ed006c07e6a4e95ef5bf09a
https://etherscan.io/tx/0xd5d9950e901cb5fff8e44af4e41f293ccf73e2c8d20e856a7b6e692289bd0f8e
2. Stars Arena — $3.0m Lost (Reentrancy)
Stars Arena, a prominent platform on the Avalanche blockchain, was compromised by a reentrancy attack, leading to a loss of $2,974,530, equivalent to 266,102 AVAX. The attacker executed a sophisticated scheme on October 7, 2023, involving a malicious contract that facilitated the reentry during a function call on the Stars Arena contract. This allowed the extraction of funds and their distribution across numerous addresses. The technical intricacies of the exploit, particularly the manipulation of the sellShares function through a malicious block height parameter, underscore the advanced nature of the threat actors targeting DeFi protocols.
Block Data Reference
Attacker Address:
https://cchain.explorer.avax.network/address/0xa2ebf3fcd757e9be1e58b643b6b5077d11b4ad7a
Malicious Transaction:
https://cchain.explorer.avax.network/tx/0x4f37ffecdad598f53b8d5a2d9df98e3c00fbda4328585eb9947a412b5fe17ac5
Malicious Contract:
https://cchain.explorer.avax.network/address/0x7f283edc5ec7163de234e6a97fdfb16ff2d2c7ac
Funds Distribution Transactions:
https://snowtrace.io/tx/0x8f5b2e8869260d6854ce4c93f58dfcbf6e8fb18b96c3e76db1eeb6dce0ef9fb1
Some of the Stolen Funds Holders:
https://cchain.explorer.avax.network/address/0x9b5ec83e5b9f124056596b7e9cbc08db622d418d
https://cchain.explorer.avax.network/address/0xded436c23e42312f866675b4980d0b1633c56b3e
3. IVY — $1.8m Lost (Rugpull)
The DeFi community witnessed a calculated exit scam with the IVY token rug pull on October 16, 2023. The fraudulent act involved the removal of liquidity and the sale of tokens totaling $234,361. The orchestrated liquidity drain from PancakeSwap’s LP pool, followed by the sale of tokens across sixteen transactions, led to an aggregate loss of $1,820,319. The deployer’s renouncement of ownership prior to the scam played a critical part in enabling the theft, which culminated in the funds being converted to USDT and obscured through transfers to various addresses.
Block Data Reference
Deployer Address:
https://bscscan.com/address/0x00B3aa7E0BE8D25f5DfCA7Aa0cE0a81859534B23
Scammer Addresses:
https://bscscan.com/address/0x5c30d0a96820dc371e9Ac733AB5E4673723de64b
https://bscscan.com/address/0xee5797EC3aaD86DD0a802Fa0FEAB942aa8523cC5
Liquidity Removal Transaction:
https://bscscan.com/tx/0x86761605f6a507a69a6329851261e7a1d9ffe3ac699238759a11bb3a456d60ec
4. FSL — $1.7m Lost (Rugpull)
FSL, another BEP20 token listed on PancakeSwap, suffered a rug pull on October 10, 2023, resulting in a significant loss of $1,681,340. The exploit was initiated by the deployer, who minted and transferred 97 million FSL tokens to a scammer’s address. These tokens were subsequently sold, converted to USDT, then BNB, and finally sent through Tornado Cash—an anonymizing service, thereby complicating the traceability of the stolen assets.
Block Data Reference
Deployer Address:
https://bscscan.com/address/0x281b8cb2AE64cd14501fc7Bcd2545be2836B173D
Scammer Address:
https://bscscan.com/address/0x7249B903DA533358c897784438b87Bc94b402352
Liquidity Removal Transaction:
https://bscscan.com/tx/0x792515002eaeb73da6ca36b535ae50b3e95c69b74c1a39beea90ff31c2bed5c1
Tornado Cash Transactions:
https://bscscan.com/tx/0x0d7afb6085443cbdf085afe649a97673eec84e1a8f03959b65c1c937817b7dae
https://bscscan.com/tx/0x7cbba5f46dfb79e36fd8d1acca1cd911f974197d0cc544e440d915703297415e
5. Safereum — $1.3m Lost (Reentrancy)
The SAFEREUM token project experienced a rug pull on October 24, 2023, when a scammer drained liquidity pools on UniSwap, leading to losses of $1,306,583. The exploit involved the unlocking and selling of 95 billion SAFEREUM tokens across two UniSwap pools. The scammer employed multiple external owned accounts (EOAs) to distribute the funds and engaged services like FixedFloat Exchange and MetaMask to exchange a portion of the stolen funds to USDT, dispersing them to further obfuscate the trail. The loss, equivalent to 732.39 ETH, reflects the ongoing vulnerability of DeFi liquidity pools to such predatory tactics.
Block Data Reference
Deployer Address:
https://etherscan.io/address/0xf7979E7FB772e8dcB95858C2A0BB6e4F81934A6b
Scammer Address:
https://etherscan.io/address/0x67c8423a7709adb8ed31c04dcbb0c161637b807f
Unlock Transaction:
https://etherscan.io/tx/0x7fd3ad139e759e3ccffe6a3e09527432536a28f94d159574daa8cf8d3196efb9
Liquidity Draining Transactions:
https://etherscan.io/tx/0x880c9ba14c8fd11ad668066ce6d9490f8dcfac6a28f48b17101032a3427cc5e2
https://etherscan.io/tx/0x7ea754306e87882a35265bdf23ac470bbe7ede4b07126e7ea2f516b7d3a14ecf
https://etherscan.io/tx/0x98568ec9f66f5365e63293be3a6d71b79cd5ae2c8134c1c06859b22c47a10c7c
https://etherscan.io/tx/0x98568ec9f66f5365e63293be3a6d71b79cd5ae2c8134c1c06859b22c47a10c7c
Funds Transfer Transaction Example:
https://etherscan.io/tx/0xc3c7100c7137bfa46958d20f574a4e506d1a94a56d9d080ab2644f4674a718c5
FixedFloat Deposit Transaction Example:
https://etherscan.io/tx/0x4c2a90d4daf74ac65794ae98ddc9f4e442d6142d9b6e645f2b9a5689f02da12f
6. Hope Lend — $835k Lost (Front Run Attack)
Hope Lend, a DeFi lending protocol on the Ethereum blockchain, faced a front run attack on October 18, 2023, culminating in a theft of $834,616, equivalent to 528 ETH. The attacker capitalized on a WBTC decimals and rounding issue within the protocol. However, in a dramatic turn of events, the attacker’s plan was thwarted by a miner extractable value (MEV) bot, which front-ran the initial exploitative transaction. The aftermath of the attack saw the MEV bot dividing the stolen funds—sending half as a bribe to the block producer, while redirecting the remaining half to another external owned account (EOA) and eventually to a MultiSigWallet.
Block Data Reference
Attacker Address:
https://etherscan.io/address/0xa8bbb3742f299b183190a9b079f1c0db8924145b
Original Attacker:
https://etherscan.io/address/0x1f23eb80f0c16758e4a55d48097c343bd20be56f
Funds Holder as of Oct 26, 2023:
https://etherscan.io/address/0x1343d353a95c8a00efddc4cf6cebe36b413164ef
Malicious Transaction:
https://etherscan.io/tx/0x1a7ee0a7efc70ed7429edef069a1dd001fbff378748d91f17ab1876dc6d10392
7. Eigenlayer (Fake Token) — $835k Lost (Rugpull)
The fake EigenLayer token, a BEP20 impersonator of a legitimate project, orchestrated an exit scam that saw liquidity removals totaling 821,232 USD, approximately 3,802 BNB, from PancakeSwap between September 14 and October 2, 2023. The deployer systematically removed liquidity in twenty-seven distinct transactions, subsequently funneling the ill-gotten gains to various addresses.
Block Data Reference
Deployer Address:
https://bscscan.com/address/0x12296f35e7B58F47Bb78C3fB4d1ba943c1270E85
Scammer Addresses:
https://bscscan.com/address/0xF6Da79E6E590799e744500798670529E9BA360ba
https://bscscan.com/address/0xAae3DA50681fD263474A611385f8EF950d4Dacd1
Liquidity Removal Transaction:
https://bscscan.com/tx/0xec9b2a71bb3320e5d8b4f4fcdf3b4be5b64d6a46365a306bcb5687efe5a59b53
8. Linea (Fake Token) — $741k Lost (Rugpull)
LINEA, an ERC20 copycat token, experienced a rug pull on October 25, 2023, where the scammer successfully removed liquidity worth $740,809 from the UniSwap pool.
The fraudulent actor manipulated token prices through fabricated transactions before depleting the liquidity pool, which also doubled as the token contract. The stolen funds, totaling 403.89 WETH, were then laundered through Tornado Cash, complicating the traceability of the assets.
Block Data Reference
Deployer Address:
https://etherscan.io/address/0x5Ac6737bD66d870cf52e51d95976E59C9b6DAC99
Liquidity Removal Transaction:
https://etherscan.io/tx/0x4ab6ec871ee08d408f1e5af97450af37b052e8df633074f1687d78c9eb6e4ced
Tornado Cash Deposit Transactions:
https://etherscan.io/tx/0x7969c1a06b2e8094c11cb651b2bc3bb38400c552042e1475e63fbaec2eb8be03
https://etherscan.io/tx/0xe365eb799af17ee813fe75a159ebd7cd02f467f076ed2cfa0b134ecae29b1b00
9. MEME (Fake Token) — $188k Lost (Rugpull)
On October 26, 2023, the MEME ERC20 token fell victim to a rug pull by the deployer, resulting in a total loss of 105.27 WETH, valued at approximately $188,095. The deployer executed the rug pull by offloading a substantial number of MEME tokens and draining the UniSwap liquidity pool. The stolen funds were then moved to a scammer’s address, followed by a dispersal of 98 ETH to 50 different addresses using Dispers.app.
Block Data Reference
Deployer Address:
https://etherscan.io/address/0x8697f6BfC933ddbCd225900A93B2f7DD6d8F9bf5
Scammer Address:
https://etherscan.io/address/0x4649F62750775220f33E0376a3CceB82f69f9527
Liquidity Removal Transaction:
https://etherscan.io/tx/0xd7e09b71e7945a4cc1f2592bc94eb58343672ce08cc3d35b524090f09fb44e1d
Stolen Funds Distribution Transaction:
https://etherscan.io/tx/0x2f8fda5dd5ce832747aa16124516ece0805a604fc89604ed3a02639d8171d4cb
10. BIGTIME Token — $169k Lost (Rugpull)
The BIGTIME token, a BEP20 asset on PancakeSwap, was the target of a rug pull on October 13, 2023, with losses amounting to $168,699. In this exploit, the scammer, having received an initial 0.055 BNB from Binance, swapped BIGTIME tokens for WBNB. The accumulated funds, 819.9 BNB in total, were then distributed among multiple addresses. Investigations suggest that the scammer was not directly associated with the deployer but may have exploited a deliberately included backdoor in the contract.
Block Data Reference
Deployer Address:
https://bscscan.com/address/0x2776B1Fa501F9617f0bddAfb413659BAFBC7F15D
Scammer Addresses:
https://bscscan.com/address/0x2f154868760eFEd95f7D551F77454a78340bfF8C
https://bscscan.com/address/0x3f04768Eaf45f1F5961857c0216E36A49Cc704ED
https://bscscan.com/address/0x336dd91Ce7f72d7Ae07a70100247e49f769ABb11
Conclusion
The considerable financial repercussions experienced in October 2023 underline the essential requirement for reinforced risk management protocols and increased caution within the Decentralized Finance (DeFi) sector. The persistence of high-profile exploits, particularly rug pulls, serves as a stark reminder of the sophisticated risks that pervade this innovative financial space.
At De.Fi, we are keenly aware of the significant role that informed guidance and support play in safely navigating the intricate DeFi ecosystem. Our commitment to our users extends beyond mere advisories; we are steadfast in our mission to provide robust resources and up-to-date data that enable and enhance the decision-making capabilities of our clientele. To this end, we provide user-friendly tools like the De.Fi Shield and De.Fi Scanner, which allow users to quickly identify risky contracts and avoid further investment.
About De.Fi
De.Fi is an all-in-one Web3 Super App featuring an Asset Management Dashboard, Opportunity Explorer, and home of the world’s first Crypto Antivirus powered by the largest compilation of hacks and exploits, the Rekt Database. Trusted by 600K users globally, De.Fi aims to drive DeFi adoption by making the self-custody transition as simple and secure as possible. Backed by Okx, Huobi, former Coinbase M&A, and used by large companies worldwide, including University College London and Coingecko.
Website | Twitter | De.Fi Security | Rekt Database
October 2025 saw a total of $38.63 million lost across nine distinct security incidents in both centralized and decentralized platforms.
The third quarter of 2025 marked yet another turbulent period for the DeFi and wider crypto ecosystem, with $434,124,000 lost to exploits, scams, and security failures across both centralized and decentralized platforms.
June 2025 witnessed another alarming month for Web3 security, with a total of $114,768,000 lost during 11 separate attacks
May 2025 saw both DeFi and CeFi security once again under attack, with $275,953,000 lost across just 8 recorded incidents
April 2025 witnessed a large escalation in exploit volume and value, with a massive $5,919,684,000 being stolen in 10 confirmed events.
Q1 2025 marked one of the worst quarters in blockchain exploit history, with total recorded losses topping $2,052,584,700 across 37 incidents
© De.Fi. All rights reserved.